Power-specific Lateral Security Isolation Device
A network security device with physical isolation capabilities, characterized by easy operation, high performance, and high reliability.
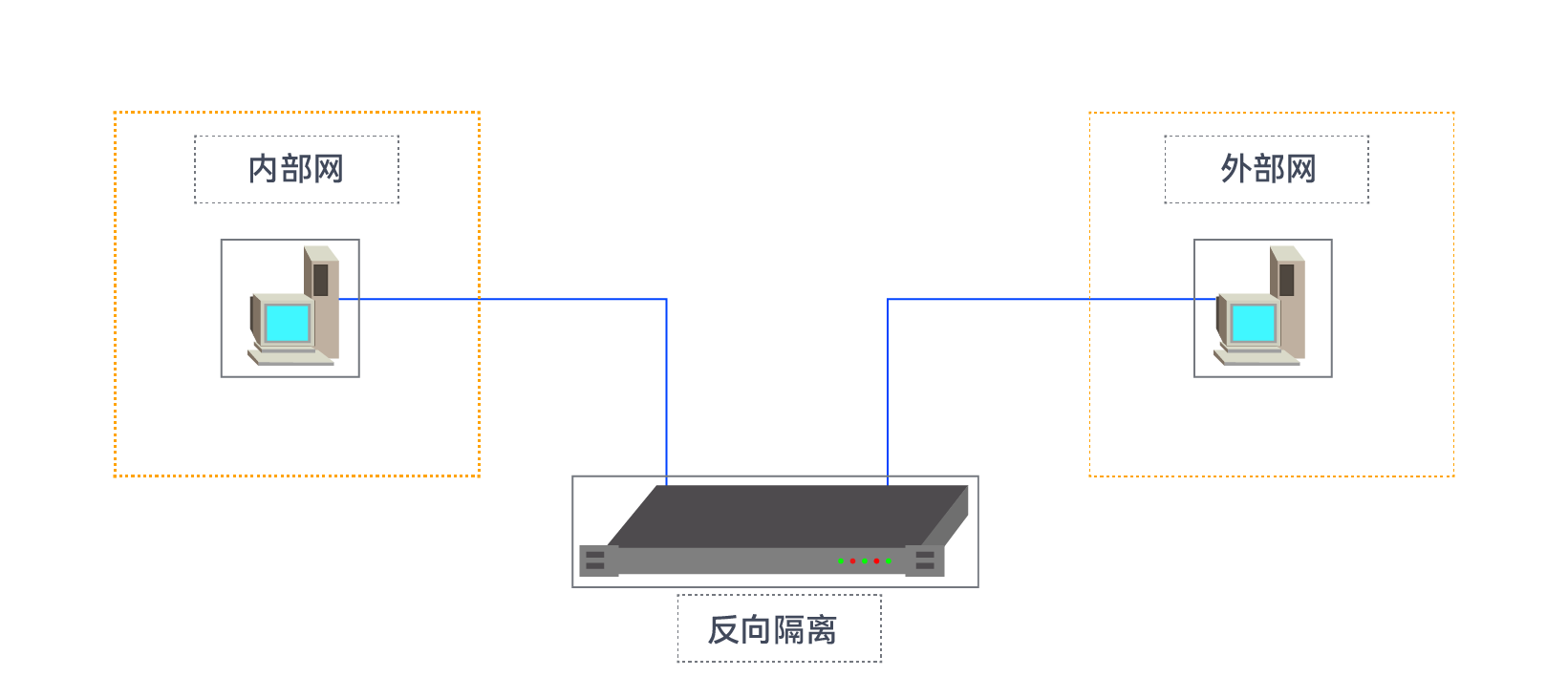
Reverse isolation adopts a combination of software and hardware security measures. The hardware employs a "2+1" structure to achieve physical isolation through a secure island device for communication.
While ensuring network transparency, it utilizes non-binary inspection technology and CIM-E language format checking to filter illegal packets.
Reverse isolation is paired with a transmission service to achieve secure transmission of trusted data from the external network to the internal network. During transmission, the sending-end service encrypts external network data. After the reverse isolation external network receives the packet, it performs comprehensive filtering based on security policies, decrypts and performs data validation. Only packets that pass validation can enter the internal network, thereby ensuring the security of the internal network system and guaranteeing that trusted data can enter the internal network under network isolation conditions.
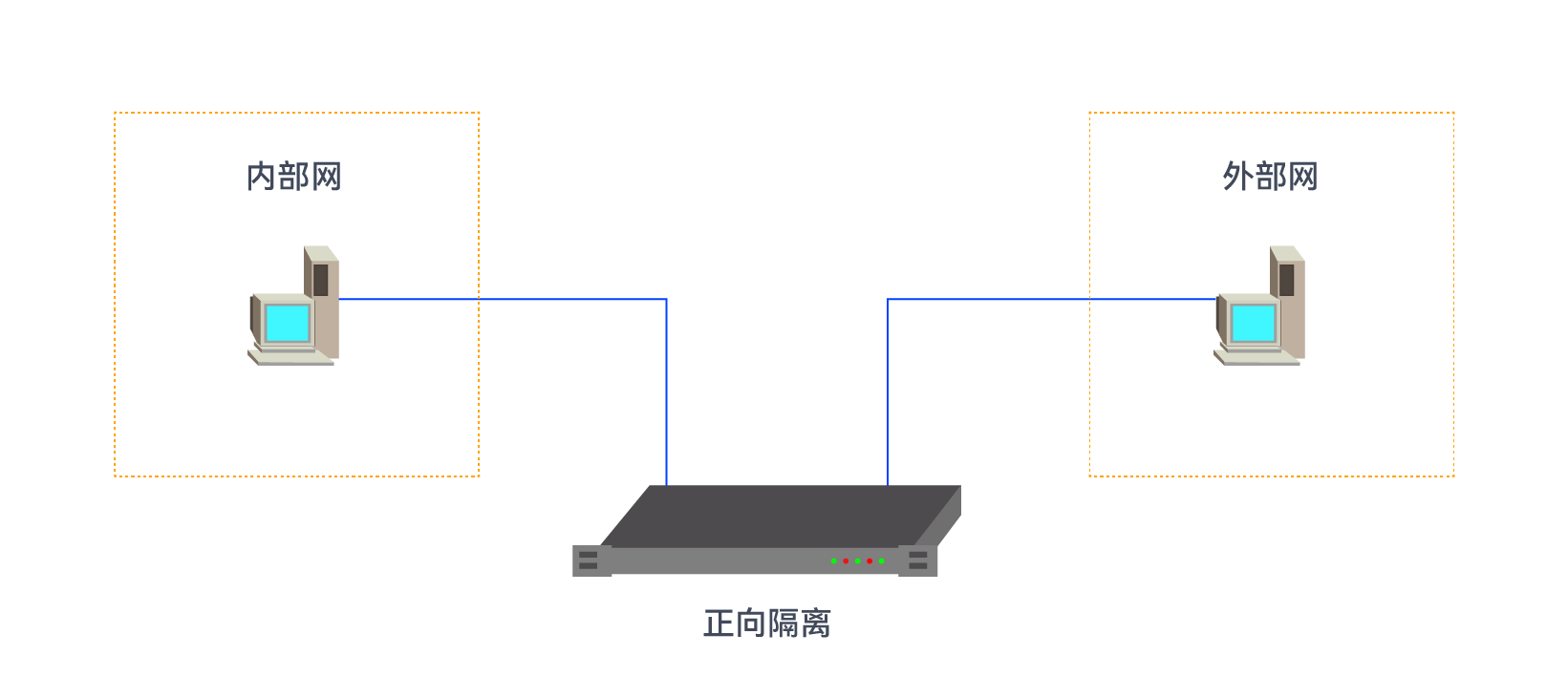
Forward isolation adopts a combination of software and hardware security measures. The hardware employs a "2+1" structure to achieve physical isolation through a secure island device for communication. In terms of software, it utilizes integrated filtering, access control, and application proxy technologies to achieve isolation at the data link layer, network layer, and application layer, thereby filtering illegal packets while ensuring network transparency.